Being More Human in a World of Marketing Robots
Cut through the cybersecurity noise with our guide. Learn authentic engagement, strategic partnerships, and interactive experiences for real results.
The Risk Management Tool from Heaven

Elevate cybersecurity with quantitative risk assessments. Learn how technology bridges the gap between CISOs and executives for smarter, real-time decisions.
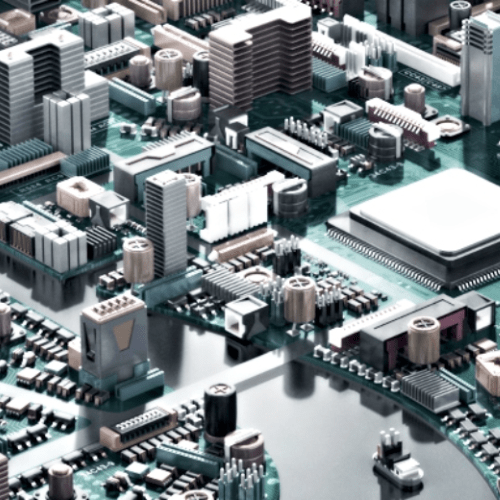
Here Comes 5G
Navigating 5G’s cybersecurity maze? Learn key vulnerabilities and steps to protect your network in the fast-paced world of 5G technology.
7 Steps to Prepare for Cyberattacks During Elections

Safeguard your business this election season with our 7-step cybersecurity guide. Learn to protect critical assets and respond to cyber crises effectively.
Five Years Forward Inside a Zeitgeist of Transition
Discover future trends in tech and business for the next five years. Learn how CIO roles, digital ethics, and emerging technologies will redefine the landscape.
Threat Report: The State of Cybersecurity Today

Explore why current cybersecurity methods are failing and how the dark web and disinformation campaigns are shaping new threats. Stay ahead of risks.
Chinese Ambition and Our Existential Threat
Discover the risks of tech business in China. Learn how the Chinese Communist Party’s tactics impact US IP and cybersecurity. Act now, tomorrow may be too late.
Redteam Testing Is Critical but Results Require Action

Discover how a $3B restaurant chain’s oversight led to a major data breach. Learn key cybersecurity lessons to protect your business from similar risks.
Enterprise Risk Management: A Branch of Organizational Behavioral Science

Unlock board-level risk management insights. Our groundbreaking study offers strategies for governance and ERM in today’s volatile landscape.
Why Security Frameworks Matter – A Different Perspective

Discover how cybersecurity frameworks like NIST CSF simplify compliance, bridging the gap between technical “hows” for better security management.
Decision-Making in a Time of Stress and Chaos
Master the art of quick decision-making in cyberwarfare. Learn the 40/70 rule and how military strategies can help you stay ahead in cybersecurity.
The Difference Between HL7 and APIs: What CIOs Need to Know to Succeed with the 21st Century CURES Act Final Rule

Discover how the 21st Century CURES Act reshapes healthcare data access. Learn key technologies CIOs need for secure, patient-centric data interchange.
Two Great Security Professionals Reflect on One Human Factor in Cybersecurity
Dive into a candid cybersecurity discussion with CISO Chris Roberts and Paige Thompson. Learn how COVID-19 exposes gaps in tech and human behavior.
We Spend Lavishly on Systems and Software-Centric Security but Nothing on Hardware – Why?
Discover hidden hardware vulnerabilities across major vendors. Learn how Sepio Systems fortifies your cybersecurity strategy with real-time threat prevention.
Your Perspective is Dictated by Your Mental Models

Discover how the pandemic elevates cybersecurity roles and why a mindset shift is essential for tackling new challenges. Learn to adapt and stay ahead.
A Cybersecurity Education Proposal
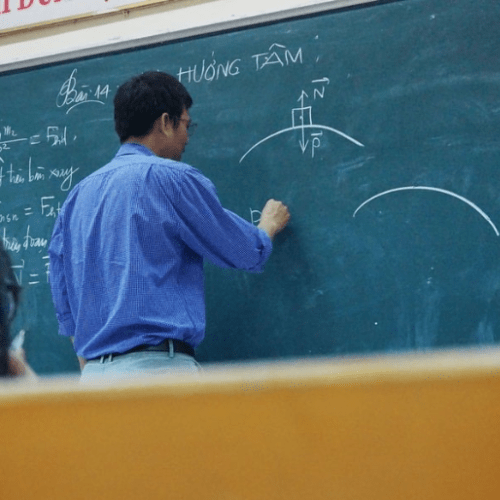
Learn about the skills gap, policy failures, and the urgent need for a national strategy.
A Cybersecurity Education Conundrum
Discover why the U.S. is falling behind in cybersecurity education and learn about the skills gap and the urgent need for a national strategy.
Artificial Intelligence meets Cybersecurity
Discover how AI is reshaping cybersecurity. Learn about new challenges for infosec officers and the urgent need for ethical and governance frameworks.
Cybersecurity and Board Oversight: Bike-shedding Gets in the Way

Discover why board members lag in cybersecurity readiness and how this gap affects investment and compliance.
The Impact of Human and Environmental Factors on Information Security

Discover how human and environmental factors impact cybersecurity. Harness team behavior for effective defense against cyber threats.
The Cybersecurity Imperative of Protecting Critical Infrastructure

Discover the rising cyber threats to global critical infrastructure. Uncover vulnerabilities and learn how layered security and new tech can bolster defenses.
The Value of a Growth Mindset in Times of Uncertainty

Learn how shifting from a fixed to a growth mindset can make your organization agile and resilient against evolving cyber threats.
The Growing Threat from Connected Devices

Many cybersecurity analysts have warned of the rapidly emerging threat from an expanded IoT space. As you have noticed, it appears we are not only failing to improve our cybersecurity defenses, but recent data suggests we are falling even further behind while the bad guys are running ahead. We know that cybercrime is expected to […]
Viewing Proactive Cybersecurity Through the Lens of a Warrior Mindset

Discover how a Warrior Mindset can revolutionize your cybersecurity strategy, mental tenacity and after-action critiques can prepare your for any cyber threat.
A Quantified Approach to Cybersecurity Risk Assessment

Explore why traditional Cybersecurity Risk Assessment methods fall short and how Value-at-Risk provides a real-time, dollar-based evaluation of cyber threats.
A Contextual Model of a Cognitive Risk Framework for Enterprise Risk Management

Discover how a Cognitive Risk Framework enhances enterprise risk management by blending behavioral science with advanced analytics, focusing on cybersecurity.
Fear and Loathing on the Chinese Supply Chain
Explore how compromised Chinese-manufactured motherboards affect global cybersecurity. Learn the risks posed to major companies like Amazon and Apple.
The Role of Strategy in a Cybersecurity Action Plan – Deception and Human Will

Uncover the nuanced difference between cybersecurity goals and strategies. Learn how to align your organization’s operational and secondary goals with effective cybersecurity action plans.
The Argument for Cybersecurity Fundamentals – and Outside Help

Discover why basic information security hygiene is crucial in defending against evolving cyber threats like Crypto jacking and Crypto mining.
Public and Private Sector Partnerships Addressing COVID-19 Are A Model for Cybersecurity
Covid-19 crisis has fostered unprecedented public-private partnerships to combat the pandemic, how this collaboration model can be applied to cybersecurity.