Not Secure?
Explore the link between ‘Not Secure’ websites and cyberattacks. CIP’s research shows poor PKI management risks your security. Learn Zero Trust strategies.

Explore the link between ‘Not Secure’ websites and cyberattacks. CIP’s research shows poor PKI management risks your security. Learn Zero Trust strategies.

IKEA hit by a widespread cyberattack affecting servers and spreading malware. The incident raises urgent questions about customer data security.

Explore the journey from early firewalls to today’s complex security needs. Learn why a multi-layered approach is essential for modern cybersecurity.

SunWater’s 9-month cyberattack exposes glaring security flaws, putting data and infrastructure at risk. A must-read for C-Suite and cybersecurity pros.
Learn how to fortify your cyber defenses through cognitive readiness and agile governance. Discover why traditional methods fail, which approaches are essential.

Explore the alarming rise of 2021 ransomware attacks and its complex financial network. Learn how regulations like OFAC are stepping into curb this cyber menace.

This blog explores the challenges CISOs face in a complex tech landscape and why a holistic approach is crucial for success.
CyberTheory’s Q3 2021 Review highlights rising complexity in open-source supply chain attacks. Steve King advises a rethink of cyber defense strategies.

Explore the rise of insider threats in cybersecurity and how Zero Trust architecture can mitigate risks.
In a “flashing red” cybersecurity state, defenses fail as threats rise. Explore why Zero Trust is urgent amid outdated systems. Act now.
As further proof that we are not only losing this cybersecurity war, we seem to

Explore the future of cybersecurity: rising threats, cloud vulnerabilities, and deepfake tech. Learn what’s at stake for enterprise security.
The human factor is an organization’s most valuable asset and its greatest vulnerability. However, it can be developed into its strongest security control.

Explore why the U.S.’s $18.78B cybersecurity budget falls short. Learn about the lack of unified defense and the urgent need for a robust strategy.

The evolution of cybersecurity and the challenges facing today’s CISOs. Learn why traditional marketing strategies are failing and how to adapt for the future.
Explore why big data isn’t enough for cybersecurity, how contextual analytics offers a solution, and the reasoning models make threat defense more effective.

Explore the intersection of digital transformation and data security. Learn why mental readiness is key to safeguarding your organization’s digital assets.
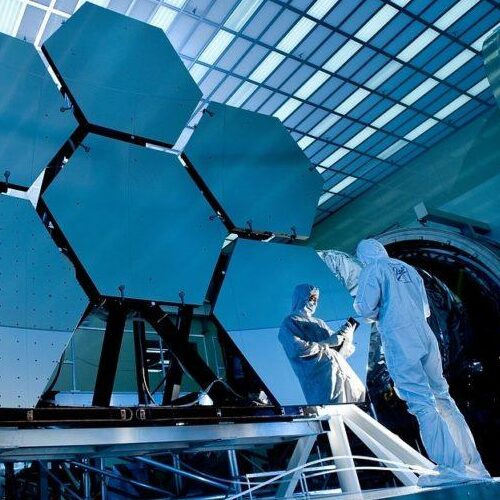
Discover how Industry 4.0 merges physical and digital worlds, elevating cybersecurity risks and solutions. Learn the role of R&D and public-private partnerships.

Uncover China’s growing influence in U.S. tech and cybersecurity. Learn about their strategic investments and the inadequate response in this eye-opening blog.

Navigating the complexities of the “Essential Eight” in cybersecurity for large enterprises. Are we chasing an unattainable goal?

Explore why network-based cybersecurity falls short in protecting critical infrastructure and how sensor monitoring offers a more robust solution.
Uncover the truth about Huawei’s cybersecurity practices and ownership structure, common misconceptions and highlights Huawei’s commitment to security.

Uncover China’s growing cyber threats to U.S. critical infrastructure and the urgent call for a fortified cybersecurity strategy.

Discover how NY’s 23 NCRR 500 regulation setting new cybersecurity standards for financial firms, navigate risk assessments and avoid becoming the next Equifax.
The evolving challenges and vulnerabilities in smart grid architectures, the rise of ransomware, RCEs, and how to secure your enterprise against cyber threats.
Uncover the link between cybersecurity and economics as system models and ideologies. Learn why the fight against cybercrime is at a critical juncture.

This post focuses on the top 5 macro-drivers of cyber risk and offers practical strategies for effective defense.
Learn the unsolvable problem of cyber espionage and its impact on global politics and security. A must-read for understanding challenges in a connected world.

Explore the limitations of big data in cybersecurity, contextual analytics and learn about reasoning models and the future of AI in cybersecurity.

Discover why financial controls fall short in cybersecurity and how design thinking can offer a transformative approach. Inspired by Wonder Woman’s journey.
Cybersecurity is in our DNA.
CyberTheory is a full-service cybersecurity marketing advisory firm. Our strategies increase lead generation rates for B2B organizations. Our professionals leverage insider intelligence and proprietary data models for optimal outcomes.
info@cybertheory.io